Recently, huge sites like Daraz, Foodmandu, Vianet, Mercantile were hacked and many users suffered a data breach in Nepal. The commodity, not the century have always changed throughout history, oil ruled the 20th century it passed on its crown to data. Data and flow of data basically run the world and it’s of extreme value in today’s day and age. With such large data traffic globally a problem of a data breach is lurking. A data breach is an unintentional or intentional leak of Private/confidential user information to an untrusted environment. Data breaches can include financial information, health data, personally identifiable information, trade secrets and so on.
In recent years with development in internet technology cybersecurity has been a major issue in Nepal. The nation has succumbed to data breaches time and again. Recently our cyber network has become victims of two major data breach while the country is going through a nationwide lockdown. First a reputable online food delivery service Foodmandu was hacked where over 50,000 user’s data was stolen from the company’s database. The user with the username of “me.mugger” has claimed to have hacked the service according to a Twitter handle. The hacker went onto explain the reason for hacking was to show how vulnerable our security really.

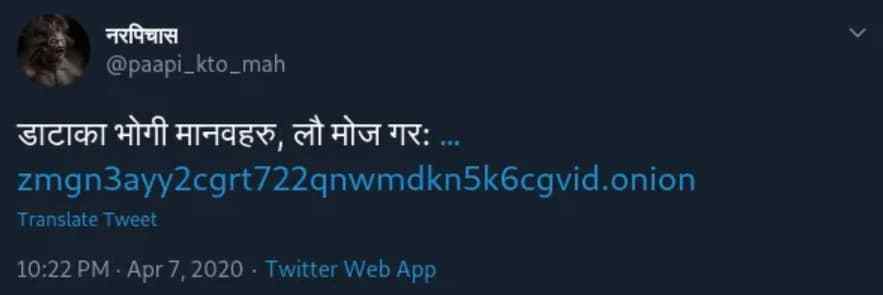
Before the incident that befell on Foodmandu was put to rest another major ISP Vianet was hacked. The scale of the data breach was even larger in comparison, Over 170000 user data was leaked from the hacker’s Twitter account. The data leak has happened from a twitter handle “नरपिचास” (@paapi_kto_mah). The Nepali tweet was “डाटा भोगी मानबहरु लौ मोज गर” which can be roughly translated to “Enjoy Data hungry people!!”. The data dump is done by hosting it in “Onion network” making it impossible to trace.
Also Read: How to apply for e-Pass?
Vianet acknowledges the incident with the breach of its information system and has issued an apology for the discomfort and the inconveniences faced by the user. The company have also claimed to have identified the source of such data spill and has assured the users that necessary steps have been taken in order to mitigate ta potential backlash from the attack. Such attacks are the example of how our cybersecurity has vulnerable points which can be exploited leading up to something even more unfortunate. More companies are falling prey to such breaches.
As of end users, we should be aware of our cyber activities and take necessary steps to strengthen our personal data security. Every individual effort from the end user side makes the overall cybersecurity stronger. As a wall of as strong as the bricks laid to build it.

